
Every unused licence is an unlocked door. Most organisations have no idea how many doors they have left open.
March 2026 | 6 min read
At a Glance
For most of IT history, the perimeter was physical. The firewall. The VPN. The network edge. That model ended when organisations moved to cloud-first infrastructure and Microsoft 365 became the operating system of the enterprise. Today, the boundary between inside and outside is not a network edge. It is a set of credentials.
This shift has direct and underappreciated consequences for how organisations manage their Microsoft 365 licence estate. Microsoft 365 Licence hygiene, the discipline of ensuring that every account holds only the access it actually needs, is not a cost management exercise. It is an identity security Microsoft 365 exercise. And most organisations are failing at it.
1. The Perimeter Doesn’t Exist Anymore
For most of IT security’s history, the perimeter was physical. The network edge, the firewall, the VPN. Keep attackers outside the boundary and your data stays safe. That model died when organisations moved to cloud-first infrastructure, remote working became standard, and Microsoft 365 became the central operating system for most of the enterprise.
Today, the perimeter is identity. The boundary between “inside” and “outside” is no longer a network edge. It is a set of credentials. If an attacker has a valid username and password, they are inside. They do not need to breach a firewall. They log in.
This is not a new idea in security circles. But the operational implications for Microsoft 365 environments are still not well understood. Identity security Microsoft 365 is treated as an authentication problem: deploy MFA, use conditional Microsoft 365 access control, enforce strong passwords. These are necessary. They are not sufficient.
The deeper problem is what sits behind the authentication layer: accounts that should not exist, licences that grant access nobody is monitoring, permissions that were assigned years ago and never reviewed. That is the Microsoft 365 licence hygiene problem. And it is a security problem, not just a cost problem.
2. What Licence Sprawl Looks Like from an Attacker’s Perspective
Attackers who target Microsoft 365 environments are not guessing. They are systematic. They look for low-hanging fruit: accounts that have active licences but have not generated sign-in activity for months, service accounts with broad permissions that predate the current IT team, guest accounts from contractors who finished engagements two years ago but were never removed.
These accounts are attractive for one reason. They are quiet. No one is watching them. There is no user to notice a login at 2am from an unusual location. There is no pattern-of-life data to generate an anomaly alert. An attacker who compromises one of these accounts can move through the tenant slowly and quietly, mapping out what is accessible before doing anything visible.
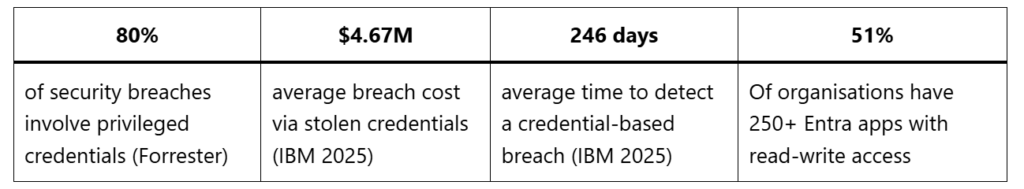
IBM’s 2025 Cost of a Data Breach Report puts the mean time to identify and contain a credential-based breach at 246 days. That is eight months of undetected activity. In a Microsoft 365 environment, eight months of access means mail, files, Teams conversations, SharePoint sites, and potentially connections to downstream systems.
The accounts enabling that access are often licenced. They appear legitimate. Microsoft native tooling does not flag them as anomalous because they are assigned active licences and sit within normal tenant structures. Only a governance layer that tracks usage against assignment would surface them as inactive and flag them for review.
Security Risk: Forrester estimates that at least 80% of security breaches involve privileged credentials. In Microsoft 365 environments, overprivileged or inactive accounts with broad access are among the most common and least monitored attack vectors. Microsoft 365 Licence hygiene is not optional. It is the first line of identity defence.
3. The Entra ID Governance Permission Problem
The credential risk extends beyond user accounts. Entra ID, Microsoft’s identity platform, manages permissions not just for users but for applications. And the application permissions landscape in most organisations is far broader than IT teams realise.
Research published in 2025 found that 51% of organisations have more than 250 Entra apps with read-write permissions assigned. 18% have over 1,000. These apps are often the product of historical integrations, test environments, and abandoned projects. Each one represents a potential access path into the tenant.
Application permissions in Entra ID are not subject to MFA. An app with a valid token can access data without a user logging in. If that token is stolen or the app itself is compromised, the attacker has persistent, quiet access to whatever the app is permitted to read or write.
Most organisations have no accurate inventory of what Entra apps exist, what they can access, or when they last ran. That is a governance gap with direct security consequences. The principle of least privilege, the foundational security concept that accounts and applications should only have the access they actually need, is not enforceable without visibility. This is exactly the kind of issue that real-time governance analytics are built to surface.
“You can’t govern what you can’t see. The organisations with the cleanest identity postures are the ones that treat licence hygiene as continuous infrastructure work, not an annual audit.”
4. How Microsoft 365 Licence Hygiene Closes the Security Gap
Microsoft 365 Licence hygiene, done properly, is identity governance. It is the continuous process of ensuring that every account in the tenant is assigned the correct access, that inactive accounts are deprovisioned, and that permissions are reviewed and trimmed to the minimum required.
This process has direct security benefits. An account that is deprovisioned immediately when an employee leaves cannot be used as an entry point. A user assigned only the features their role requires cannot be exploited to access systems outside their scope. An application with read-only access cannot be used to exfiltrate and then corrupt data.
The challenge is operationalising this at scale. Most Microsoft 365 environments have thousands of accounts, hundreds of applications, and a licence assignment history that goes back years. Manual processes cannot keep up. The licence estate changes every time someone joins, leaves, changes role, or picks up a new project. By the time an annual audit catches the discrepancies, months of exposure have already occurred.
Continuous governance automation changes the timeline. Instead of catching inactive accounts at the next review cycle, they are flagged within days of the usage signal dropping below threshold. Instead of discovering overprivileged Entra apps in a compliance audit, they are surfaced in real time as the permission inventory is maintained automatically.
5. The Regulatory Dimension: NIS2, ISO 27001, and Identity
European organisations have additional pressure beyond the security case. The NIS2 Directive, which came into force across EU member states in late 2024, requires organisations in scope to implement access control measures and lifecycle management for accounts with access to critical systems. Microsoft 365 qualifies as critical infrastructure for most organisations that depend on it.
ISO 27001, the international standard for information security management, requires documented controls for access provisioning, user registration and deregistration, and privileged access management. Auditors will ask for evidence that these controls are operating. A spreadsheet updated quarterly does not satisfy that requirement. An automated governance platform with audit trails does.
DORA, the Digital Operational Resilience Act applying to EU financial services firms from January 2025, includes specific requirements for identity and access management as part of ICT risk management. The principle is consistent: regulators expect organisations to know who has access to what, and to demonstrate that access is appropriate and monitored.
Licence hygiene is not a compliance checkbox. But getting it right is what makes the compliance evidence credible. You cannot demonstrate controlled access without a continuous process for managing it.
6. Building a Microsoft 365 Licence Hygiene Programme That Actually Works
A Microsoft 365 licence hygiene programme that reduces security risk operates on four disciplines. First, continuous discovery: a complete, current inventory of all accounts, licences, and application permissions in the tenant, updated in real time rather than at audit intervals.
Second, usage-based assessment: crossing the licence inventory against actual activity signals. Which accounts are logging in? Which users are using which features? Which applications are running? Any account or app that holds access without generating activity is a risk to investigate.
Third, automated lifecycle management: deprovisioning accounts and revoking licences at defined points in the user lifecycle. When an employee leaves, the account should be disabled and the licence recovered without requiring a manual ticket to IT. When a contractor engagement ends, guest access should expire automatically.
Fourth, privileged access review: a regular, evidence-based process for reviewing which accounts and applications hold elevated permissions, with documented justification for each. This is the control that satisfies ISO 27001 auditors and NIS2 assessors. For IT teams looking to build this visibility, real-time governance analytics make the difference between a reactive process and a proactive one.
“Licence hygiene used to be a finance conversation. Rising breach costs and regulatory pressure have made it a CISO conversation. The organisations that treat them as the same conversation are the ones building genuine resilience.”
Conclusion
Identity is the attack surface. In Microsoft 365 environments, every active account with an assigned licence is a potential entry point. The accounts nobody is watching are the ones attackers prefer.
The 246-day average detection time for credential-based breaches is not primarily a technology failure. It is a governance failure. Organisations that cannot tell you which accounts are active, which are dormant, and which have access far beyond what their role requires are organisations that will take months to notice when something goes wrong.
Microsoft 365 Licence hygiene is the foundation of identity security Microsoft 365 . Clean the estate. Know what you have. Deprovision what you do not need. Review privileges regularly. These are not complicated ideas. The complexity is in executing them consistently at scale, and that requires automation.
The security case and the cost case are the same case. Inactive licences waste money and create risk. Over-provisioned accounts inflate the cost base and expand the attack surface. Fixing both requires the same continuous governance discipline. IT teams that treat licence management as an infrastructure responsibility rather than a periodic chore will be in a significantly better security posture by the time the next credential-based attack arrives.
About TeamsFox
TeamsFox GmbH is a Microsoft 365 governance and optimisation platform trusted in over 20 countries across Europe, MENA, and Asia. The platform delivers continuous licence management, storage optimisation, governance visibility, and Copilot readiness capabilities to IT teams who need real-time control over their M365 environment. www.teamsfox.com